In the digital age, where bytes can strike as powerfully as bombs, the battlefield has expanded beyond traditional borders into the intangible realm of cyberspace. As nations race to outmaneuver each other in this invisible arena, cyberwarfare has emerged as a defining challenge of modern security. The United States, with its vast technological infrastructure and global influence, finds itself at a critical crossroads in shaping policies that balance offense, defense, and diplomacy. This article delves into the current state of U.S. cyberwarfare policy in 2025, exploring how strategies have evolved to address emerging threats, protect national interests, and navigate the complex ethical landscape of digital conflict.
Understanding the Evolution of U.S. Cyberwarfare Strategy
Since the dawn of the digital age, U.S. cyberwarfare strategy has undergone a profound transformation, adapting to the rapidly shifting landscape of global threats. Early efforts focused primarily on defensive measures-protecting critical infrastructure and military networks from intrusion. However, as adversaries grew bolder and more sophisticated, the strategic emphasis expanded to include offensive capabilities designed to deter, disrupt, and degrade hostile actors in cyberspace.
By 2025, the U.S. approach is characterized by integration and agility. Cyber operations are no longer siloed within intelligence agencies or the military alone; they are coordinated across multiple government branches, leveraging artificial intelligence, machine learning, and real-time threat intelligence. This multi-domain integration ensures a synchronized response that combines cyber tactics with traditional military and diplomatic tools.
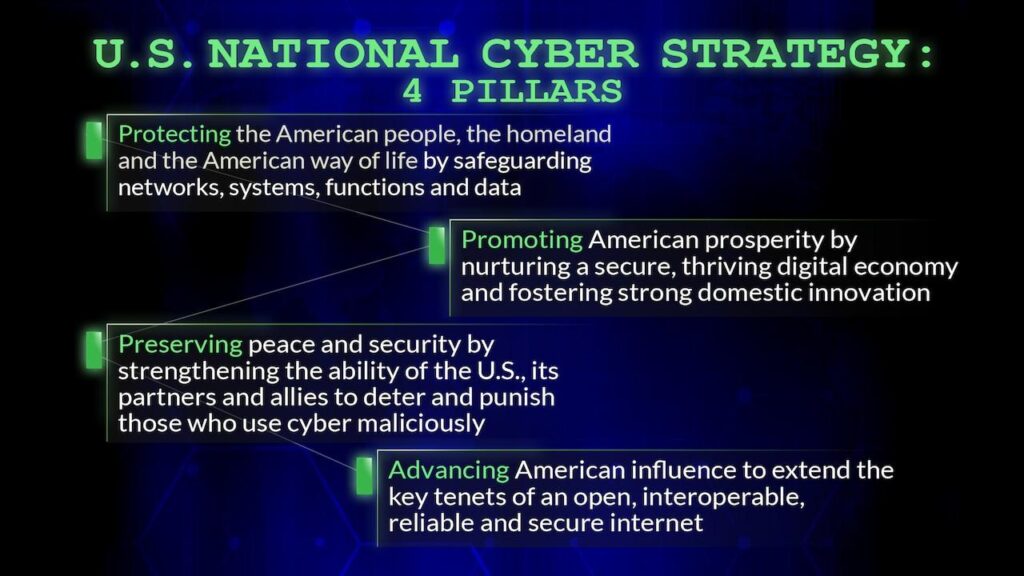
Key pillars of this evolved strategy include:
- Proactive defense: Anticipating attacks before they happen through advanced threat hunting and predictive analytics.
- Offensive deterrence: Demonstrating the capability and will to retaliate decisively in cyberspace, raising the cost of aggression.
- Public-private collaboration: Partnering with industry leaders to secure supply chains and critical infrastructure.
- International norms: Shaping global cyber norms and agreements to promote stability and accountability.
| Era | Focus | Key Development |
|---|---|---|
| 1990s-2000s | Defense & Infrastructure Protection | Firewalls, Basic Intrusion Detection |
| 2010s | Offensive Cyber Capabilities | Stuxnet, Cyber Command Establishment |
| 2020s | Integrated Multi-domain Operations | AI-driven Threat Intelligence & Public-Private Partnerships |
Assessing Current Capabilities and Emerging Threats
In today’s hyperconnected world, the U.S. faces an evolving digital battlefield where traditional defense mechanisms often fall short. Current capabilities hinge on a sophisticated blend of offensive and defensive cyber tools, bolstered by intelligence-sharing frameworks across government agencies. However, the rapid pace of technological innovation means that what is state-of-the-art today risks obsolescence tomorrow, demanding continuous adaptation and investment.
Key areas of strength include:
- Advanced threat detection using AI-driven analytics
- Robust cyber workforce training programs
- Integrated command-and-control systems for real-time response
- Collaborations with private sector cybersecurity firms
Yet, looming on the horizon are emerging threats that complicate the landscape. Quantum computing, for instance, threatens to undermine existing encryption methods, while increasingly sophisticated malware leverages machine learning to evade detection. Additionally, the rise of state-sponsored cyber proxies creates plausible deniability, blurring lines of accountability and complicating strategic responses.
| Emerging Threat | Potential Impact | U.S. Preparedness Level |
|---|---|---|
| Quantum Decryption | Breaks current encryption standards | Moderate |
| AI-Driven Malware | Adaptive and evasive attacks | Developing |
| Cyber Proxy Warfare | Obscures attacker identity | Low |
| Supply Chain Attacks | Targets critical infrastructure | High |
To maintain an edge, the U.S. must not only refine its existing capabilities but also anticipate and counteract these sophisticated threats with agility and foresight. This includes embracing next-generation technologies, expanding public-private partnerships, and fostering a culture of resilience that permeates every level of national defense.
Balancing Offensive and Defensive Cyber Operations
In the evolving landscape of cyber conflicts, the United States recognizes that a rigid focus on either offense or defense alone is insufficient. Instead, it embraces a dynamic equilibrium where proactive cyber strikes and robust defense mechanisms operate in tandem. This balance is crucial not only for deterring adversaries but also for maintaining operational readiness in an environment where the front lines are invisible and ever-shifting.
On the offensive side, precision and restraint guide actions. Cyber operations aim to disrupt adversaries’ capabilities with minimal collateral damage, often targeting critical infrastructure, communication networks, or command systems. However, these strikes are carefully calibrated to avoid escalating conflicts beyond the digital realm. Meanwhile, defensive strategies have evolved beyond traditional firewalls and intrusion detection, incorporating AI-driven threat intelligence and real-time adaptive responses to thwart increasingly sophisticated attacks.
Key elements in maintaining this balance include:
- Integrated Cyber Command Structures: Ensuring seamless communication between offensive and defensive units.
- Continuous Threat Monitoring: Leveraging AI to predict and neutralize threats before they manifest.
- Legal and Ethical Frameworks: Defining boundaries to prevent misuse or unintended consequences.
- International Collaboration: Sharing intelligence with allies to strengthen collective cybersecurity postures.
| Operation Type | Primary Objective | Example Tactic | Risk Level |
|---|---|---|---|
| Offensive | Disrupt Adversary Systems | Targeted Malware Deployment | Medium-High |
| Defensive | Protect Critical Infrastructure | AI-Driven Intrusion Detection | Low-Medium |
| Hybrid | Threat Intelligence Sharing | Cross-Agency Collaboration | Low |
Integrating International Partnerships and Norms
In the rapidly evolving landscape of cyberwarfare, the United States recognizes that no nation can stand alone. The complexity and borderless nature of cyber threats demand a concerted international response. The U.S. government has therefore intensified efforts to forge strategic alliances and embed cyber norms within global frameworks. These partnerships are not merely diplomatic gestures but foundational elements that enhance collective defense and deterrence capabilities.
Key pillars of this international collaboration include:
- Information Sharing: Real-time exchange of threat intelligence to preempt attacks and disrupt adversaries.
- Joint Cyber Exercises: Simulated operations that build interoperability and resilience among allied cyber forces.
- Norms Development: Establishing agreed-upon standards for responsible state behavior in cyberspace.
- Legal Frameworks: Crafting treaties that address attribution, sovereignty, and proportional responses to cyber incidents.
One illustrative effort is the U.S.-led coalition initiatives that promote adherence to the Paris Call for Trust and Security in Cyberspace, alongside active participation in the United Nations Group of Governmental Experts (UNGGE) discussions. These platforms serve as incubators for international consensus on cyber conduct, helping to translate abstract principles into actionable policies.
| International Partnership | Focus Area | Recent Milestone |
|---|---|---|
| NATO Cyber Defence | Collective defense and rapid response | Expanded Cyber Rapid Reaction Team (2024) |
| Five Eyes Alliance | Intelligence sharing and counterespionage | Enhanced threat data integration (2023) |
| Paris Call Signatories | Norms for state behavior | Adoption of new anti-ransomware guidelines (2025) |
While progress is tangible, significant challenges remain. Differences in national priorities, legal interpretations, and technological capabilities can slow consensus-building. Nevertheless, the U.S. continues to champion a vision where cybersecurity is a shared responsibility, grounded in mutual trust and respect for sovereignty. This approach not only strengthens defense but also shapes a more stable and predictable cyberspace for all.
Policy Recommendations for Strengthening Cybersecurity Resilience
To fortify the nation’s digital defenses, policymakers must embrace a multi-layered strategy that goes beyond traditional cybersecurity frameworks. Prioritizing public-private partnerships ensures that vital infrastructure sectors benefit from shared intelligence and coordinated incident response. By fostering trust and transparency between government agencies and private firms, the resilience of critical systems can be significantly enhanced.
Investment in continuous workforce development is equally crucial. The ever-evolving cyber threat landscape demands a dynamic talent pipeline equipped with cutting-edge skills and adaptive problem-solving capabilities. Establishing national certification programs and incentivizing cybersecurity education will build a robust cadre of professionals ready to counter sophisticated cyber adversaries.
Policy must also advocate for the integration of emerging technologies such as artificial intelligence and quantum computing to anticipate and neutralize threats proactively. Allocating dedicated funds for research and development in these areas will position the U.S. at the forefront of cyber defense innovation.
- Enhance cross-sector information sharing platforms to reduce response times.
- Mandate regular cybersecurity audits for critical infrastructure providers.
- Promote international cyber norms and cooperative defense agreements.
| Policy Focus | Expected Outcome | Timeline |
|---|---|---|
| Public-Private Cybersecurity Coalition | Improved threat intelligence sharing | 1-2 years |
| National Cyber Workforce Program | Skilled cybersecurity professionals | 3-5 years |
| AI-Driven Threat Detection R&D | Proactive defense mechanisms | Ongoing |
In Conclusion
As the digital battleground continues to evolve at a breakneck pace, the United States finds itself at a pivotal crossroads in shaping its cyberwarfare policy. Balancing the imperatives of national security, international cooperation, and ethical responsibility, 2025 marks a year of both challenge and opportunity. The path forward demands vigilance, innovation, and a nuanced understanding of the cyber domain’s complexities. While the future remains uncertain, one thing is clear: the U.S. must remain agile and resolute, crafting policies that not only defend its digital frontiers but also set a precedent for global cyber stability. In this ever-shifting landscape, the story of cyberwarfare policy is far from over-it is a narrative still being written, byte by byte.